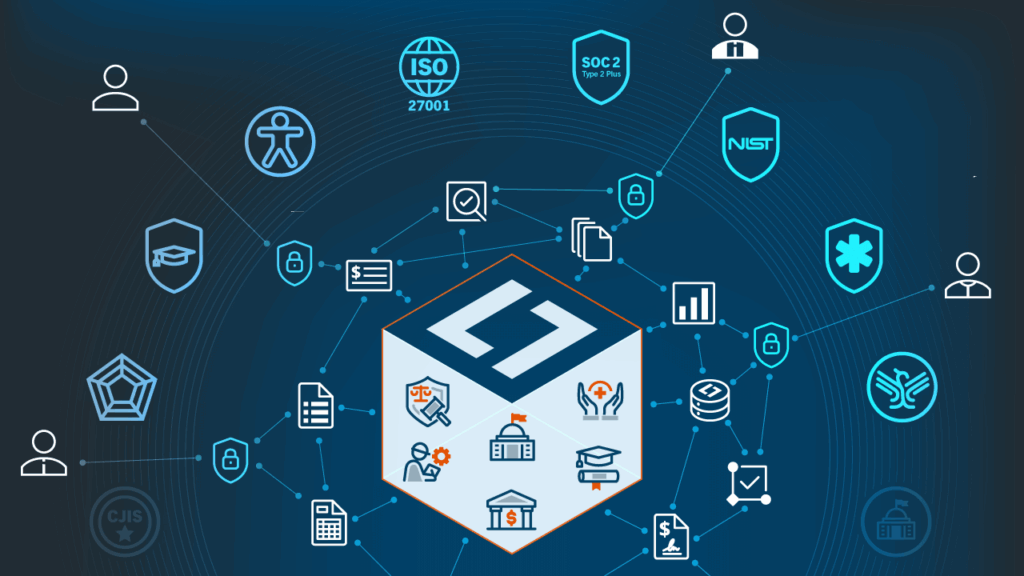
Security Certifications and Compliance Frameworks
SOC 2 Type 2 Plus
This report details the controls for Laserfiche Cloud related to the criteria for the security, availability and confidentiality principles set forth in TSP section 100, 2017 Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy (AICPA, Trust Services Criteria). To view a copy of this report, please contact us.
ISO/IEC 27001:2022
Laserfiche has obtained the ISO/IEC 27001:2022 certification for its information security management system (ISMS) within the scope defined by its Statement of Applicability, covering its suite of SaaS and self-hosted enterprise content management and process automation applications.
HIPAA
Laserfiche’s SOC Type 2 Plus covers the security requirements set forth in the Health Insurance Portability and Accountability Act of 1996 (HIPAA), provided within Title 45 Code of Federal Regulations Sections 164.308 – 312 (45 CFR Sections 164.308-312) (the Security Requirements).
Web Content Accessibility Guidelines 2.2 AA
Laserfiche has published VPATs and ACRs available for all Laserfiche Cloud and self-hosted products. Alignment to the WCAG 2.2 Level AA standard is the basis of our approach to compliance with Section 508 and EN 301 549 requirements. See accessibility details…
DoD 5015.2
DoD 5015.2 details the Department of Defense’s baseline requirements for Records Management Applications (RMA), that facilitate adequate and appropriate basis for addressing the basic challenges of managing records in the automated environment that increasingly characterizes the creation and use of records. Laserfiche Cloud records management controls are based on our self-hosted Department of Defense 5015.2 version 3-certified electronic records management capabilities.
SEC Rule 17a-4
Laserfiche features support non-alterable record archival requirements such as WORM (write once, read many) used to address SEC Rule 17a-4 for broker dealers. Beyond financial services, Laserfiche’s controls can also be applied to support records management practices for electronically stored information (ESI) requiring prevention of any unauthorized alternations or deletions of digital records.
HECVAT
Laserfiche has completed the Higher Education Community Vendor Assessment Toolkit (HECVAT) questionnaire. Contact us for more information.
NIST 800-53
Laserfiche security controls are aligned with NIST 800-53.
GovRamp Core Verified
Coming in Q3 2026
Contact us for more information.
CJIS Ready
Coming in Q3 2026
Contact us for more information.
AI Security and Governance
Laserfiche AI services are provided using AI models and services from OpenAI. For information on AI services in regions where OpenAI is not available, please contact us.
Regional data privacy requirements
Laserfiche AI addresses privacy and security standards of our current data center locations supporting GDPR (EU), CCPA/CPRA (USA), and PIPEDA (Canada) for low to moderate risk data. Our AI features are architected to support regional and industry-specific compliance needs, providing the same level of data sovereignty and protection you expect from Laserfiche Cloud.
For more information related to Laserfiche AI and data privacy, refer to the following:
- Laserfiche Privacy Notice
- OpenAI Security & Privacy
You own your data
- You retain ownership of inputs you provide. While Laserfiche owns the intellectual property rights to the outputs generated by our AI tools, we grant you a broad license to use those outputs for any of your organization’s internal business needs.
- Laserfiche does not use your organization’s data to train any internal or external AI models. Your data is used only as needed to deliver services and to meet our legal and regulatory obligations.
Laserfiche AI user prompts
Laserfiche designs its AI features with safety and security as core principles. We manage prompting risks through two layers of protection:
- Prompt-less by design: Many Laserfiche AI features, such as Document Summarization, do not use user prompts, reducing risks associated with accidental or malicious prompting.
- Enterprise-grade safeguards: For features that do accept user input, like Smart Fields and Smart Chat, we employ industry-standard protections against prompt injection. These include input filtering, validation, and other controls that keep prompts and responses within defined, limited boundaries.
Content confidentiality
Your confidential content is not accessible to other customers or unauthorized third parties. Laserfiche distinguishes between two types of data:
- Your confidential content: Laserfiche does not sell your data. Documents, files, and inputs you upload to Laserfiche are your own content.
- Usage and system data: Like most cloud providers, Laserfiche collects limited, high-level usage data (such as feature adoption and system performance metrics) to operate and improve the platform. This data is de-identified and does not include the contents of your documents or AI prompts.
Data retention
- OpenAI may store the prompts you enter or the responses you receive temporarily for up to 30 days to provide services and identify abuse. After 30 days, API inputs and outputs are removed from their systems, unless they are legally required to retain them. For more details, please refer to the OpenAI Services Agreement.
Security Controls
Below are some of the security controls Laserfiche software includes. If you have questions about a particular security solution or control, please contact us directly.
Single sign-on
Laserfiche Cloud supports single sign-on with Active Directory Federation Services (AD FS) and SAML authentication with identity providers such as Okta and Azure Active Directory.
Repository audit log
The Laserfiche Cloud repository audit log includes details of user actions, including viewing, modifying, creating and deleting documents, and similar operations on metadata and other repository objects.
Fine-grained access control
Administrators can use access rights to limit and control access to individual documents and objects. For example, security tags restrict access to documents on a document-by-document basis.
Intrusion detection
Laserfiche Cloud utilizes host-based intrusion detection systems to reduce the risk of data theft by individuals or organizations attempting to gain unauthorized access.
Access rights
Administrators can configure access rights and privileges to limit actions that users can perform across the repository based upon role assignments or group memberships.
AI governance
Laserfiche AI data is encrypted at rest (AES-256) and in transit (TLS 1.2+). Laserfiche does not utilize any of your data to train internal or external AI models.
Password policies
Laserfiche Cloud supports industry-standard password controls, such as password minimum length, complexity and history.
Penetration testing
Laserfiche engages third-party vendors to conduct external penetration testing of the Laserfiche Cloud system.
Vulnerability scanning
Laserfiche performs a vulnerability scan of backend servers that run in the Laserfiche Cloud hosting environment.
Firewalls
Laserfiche Cloud’s firewall configuration settings are regularly reviewed based on industry standards.
Repository application auditing
Laserfiche Cloud supports auditing of both access and modification of objects in repositories.

—Andrew McElrath, strategic project manager at Mille Lacs Corporate Ventures
Featured Success Story
Mille Lacs Corporate Ventures Transitions Corporate Operations to Laserfiche Cloud
Mille Lacs Corporate Ventures (MLCV), created by the tribal government of the Mille Lacs Band of Ojibwe, manages the business affairs of the Band.
Laserfiche is committed to privacy.
Our commitment
At Laserfiche, we have embraced a culture of privacy, which includes embedding privacy-by-design in our engineering efforts, and have implemented controls and policies throughout our organization. Laserfiche is a B2B company based in California. The State of California has passed strict, broad privacy regulation through the California Consumer Privacy Act (CCPA) and the California Privacy Rights Act (CPRA) while the General Data Protection Regulation (GDPR) leads the European Union’s privacy efforts. Many other countries, states and territories have implemented privacy regulations as well. Laserfiche endeavors to continually adapt and adhere to ever-evolving regulations that apply to its business.
Operational privacy
Operationally, we strive to keep our stakeholders’ data secure and retain only information we collect from you where we have an ongoing legitimate business need to do so, like providing you with a service you have requested, or to comply with applicable legal, tax or accounting requirements.
Privacy training
At Laserfiche, all employees are required to complete annual privacy training which covers applicable privacy regulations and data handling best practices.
Laserfiche documentation
In addition to what we communicate in our Privacy Notice, our Cloud Subscription Agreement with accompanying Data Processing Addendum specific to the Laserfiche Cloud platform addresses data privacy regulations including GDPR, CCPA and PIPEDA.
International transfers
For personal data transferred from the United Kingdom, the European Union and Switzerland, we provide appropriate safeguards per the Data Privacy Framework. To learn more, visit the “International Transfers” section of the Privacy Notice.
Information we collect
We collect information that you provide directly to us only for legitimate business purposes. For example, when you manage your user profile, participate in interactive features (such as the Contact Us page), request newsletters or other marketing communications, request customer support, enter login information, or otherwise communicate with us. To learn more visit the “Information We Collect” section of the Privacy Notice.
You have the right to opt-out of marketing communications we send you at any time. You can exercise this right by clicking on the “unsubscribe” or “opt-out” link in the marketing emails we send you. To learn more, visit the “How Laserfiche Uses and Shares the Information We Collect” section of the Privacy Notice.
To read our complete Privacy Notice, visit our Privacy Notice page.
Contact Us for Your ECM Needs
Whether you have product questions, support needs, or want to partner with us, we’re here to help you on your digital transformation journey. Fill out the form and a Laserfiche team member will be in touch as soon as possible.

